In our continuous effort to improve security measures and evolve to a 'least privilege' setup, we started to remove user access to disks on our IIS web servers. For most applications this turned out not be an issue, but applications using Windows Authentication started to fail. Let’s investigate what is happening and how we can fix this.
Anonymous Authentication
Let me first explain what is going on for applications that are not using Windows Authentication. These applications are configured to use Anonymous Access and the anonymous user identity is set to a specific user account or the Application pool identity. This means that only these users needs to have access to the folders on disk.
Windows Authentication
Once we move to Windows Authentication the situation gets more complex. Now the user that is authenticated needs access on disk to be able to access the site. So probably the easiest solution would be to grant the user access to disk (or just give the Everyone account access), but of course than we are throwing our ‘least privilege’ philosophy out of the window.
There are 2 possible solutions for this:
- Use the ‘Connect As’ feature
- Use the ‘authenticatedUserOverride’ setting
Connect As
- Go to your site Basic settings in IIS and click on the Connect as… button:
- Here specify a specific user instead of the application user:
AuthenticatedUserOverride
Starting from IIS 7.5 you get an extra option, you can set the ‘authenticatedUserOverride’ property to ‘UseWorkerProcessUser’.
- Go to your site and click on the Configuration Editor:
- Choose the “system.webServer/serverRuntime” section::
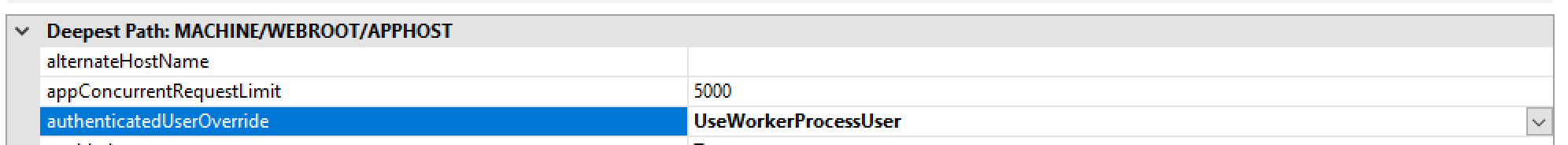
- Update the authenticatedUserOverride property and set it to UseWorkerProcessUser:
Now you are in the same scenario as with the anonymous authentication and you only need to grant specific users access to disk.
More information: jaroslad - What does the authenticatedUserOverrideUser do? (iis.net)