I’m working on a (small) open source application where I’m currently the only contributor. I setup the project so that the main branch is protected by a branch protection rule.
By using branch protection rules, you can enforce certain workflows or requirements before someone can push changes to a branch, including merging a pull request into the branch. You can view the active branch protection rules by going to Settings –> Branches (available in the Code and automation section):
In my case I had setup a rule that required a pull request before merging son that I could track and iterate on changes in separate branches. To see the specific branch rule, click on Edit next to the branch:
I liked the pull request model for this application but as a default GitHub also configured that an approval was required by at least one reviewer.
This is great if you are working with multiple contributors on a project but as I was working mostly alone on it, requiring such a review no longer made sense.
The good news is that you can easily disable it by unchecking the Require approvals checkbox:
This allows you to still use pull requests but removes the approval step as a requirement before being able to merge.
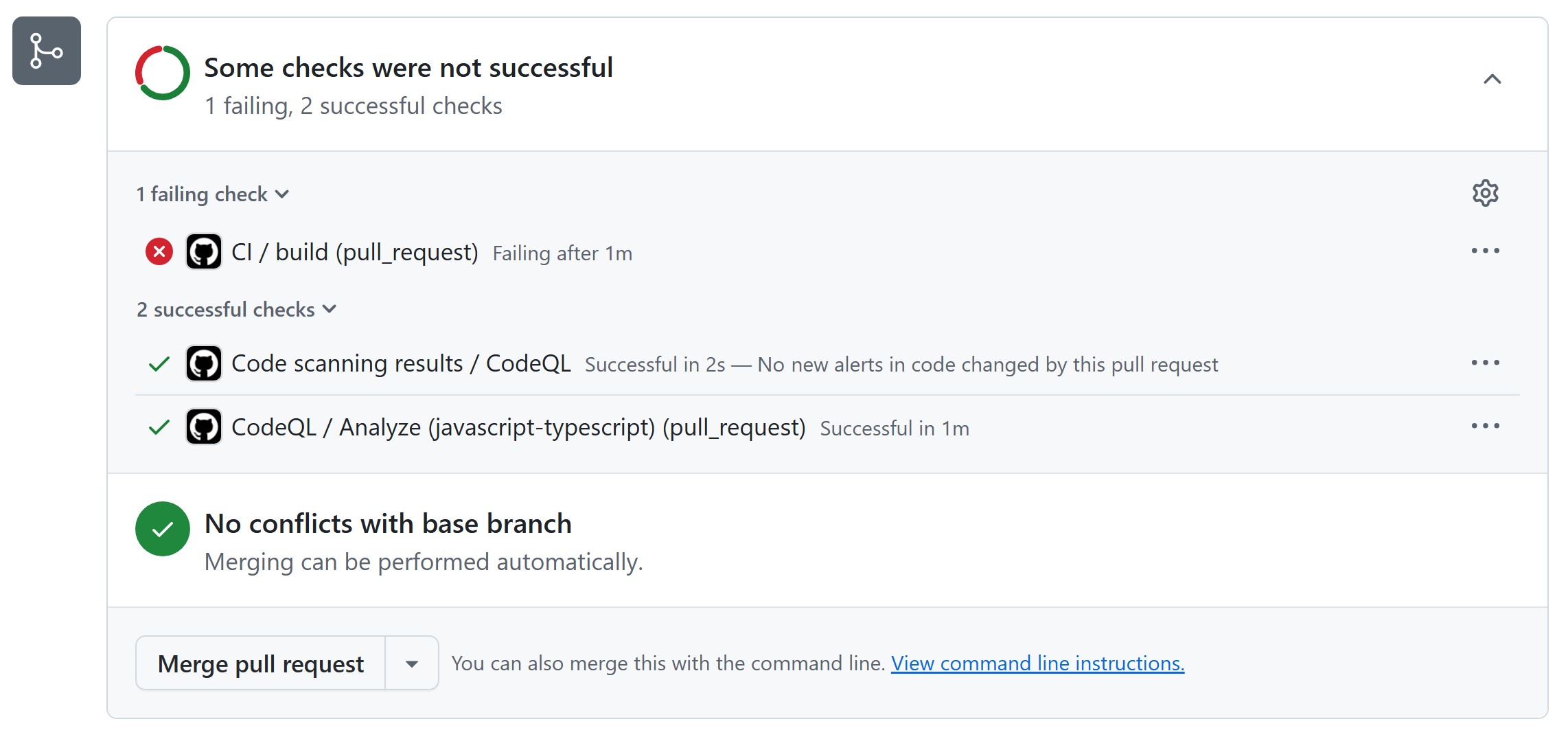
Remark: Notice that I’m still using the status checks to do some automated validation.
More information
Require pull requests without requiring reviews - GitHub Changelog