After creating a new claims rule, our ADFS instance started to return the following error message:
The new rule we created just pass an existing claim value:
c:[Type == "urn:be:vlaanderen:acm:rrn"] => issue(claim = c);
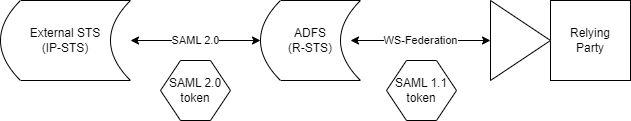
To explain why this error happened I have to give some extra context. Our ADFS instance is federated with another Identity Provider STS(IP-STS) and is acting as a resource STS(R-STS). The communication between the IP-STS and the R-STS(our ADFS instance) is done through the SAML 2.0 protocol and the tokens returned are also in SAML 2.0 format.
However the communication between the R-STS and the relying party(an ASP.NET Core application) is done through WS-Federation and the token format used there is SAML 1.1.
SAML tokens have URI (ClaimType) rules that will differ based on the version of the SAML token you intend to issue. AD FS 2.0 supports WS-Federation, WS-Trust, and SAML 2.0 protocols. WS-Federation protocol only supports SAML 1.1 tokens. WS-Trust protocol can work with multiple token types. SAML 2.0 protocol only supports SAML 2.0 tokens.
SAML 1.1 tokens have strict URI rules which state that the format must be 'namespace'/'name'. These can be constructed many ways, and here are a few common examples:
- myOrganization/myClaimType
- urn:myOrganization:claims/myClaimType
- http://myOrganization/claims/myClaimType
SAML 2.0 tokens do not have the same URI requirements, and simple names can be used. Examples:
- emailAddress
This explains the error we got.
To fix it, we have to update our claims rule to transform the incoming claim to an URI format supported by SAML 1.1:
c:[Type == "urn:be:vlaanderen:acm:rrn"] => issue(Type = http://schemas.example.be/iam/claims/rrn, Value = c.Value);