GitOps is an approach to software delivery that uses Git as a single source of truth for declarative infrastructure and application deployment. With GitOps, all changes to infrastructure and applications are made through pull requests that are reviewed and approved before they are applied to the target environment. This approach offers several benefits, including improved visibility, traceability, but the single biggest reason why you should apply a GitOps approach is (enhanced) security compared to a traditional Continuous Delivery approach.
Flux
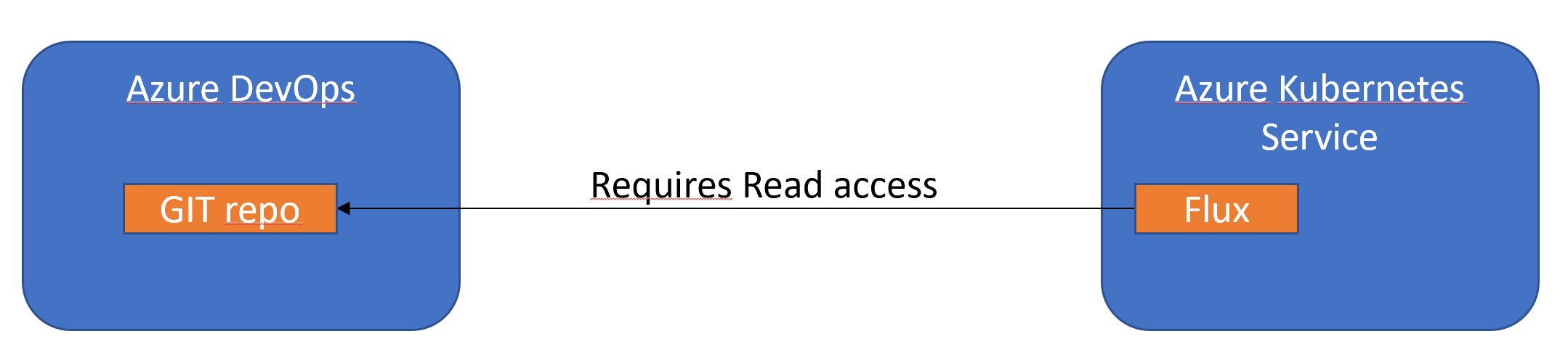
In Azure you can use GitOps in Azure Kubernetes Service (AKS) and Azure Arc-enabled Kubernetes clusters.Behind the scenes this uses Flux, a popular open-source tool set. Flux provides support for common file sources (Git and Helm repositories, Buckets, Azure Blob Storage) and template types (YAML, Helm, and Kustomize).
GitOps vs traditional Continuous Delivery(CD)
In a traditional CD setup, the CD tooling is running outside the AKS environment and the tool needs a lot of privileges on the cluster level to be able to successfully deploy the pods on the Kubernetes nodes. This is of course a security risk.
With GitOps the CD tooling(Flux in the case of AKS) runs inside the production cluster and it only needs access the code repository that is living outside the cluster. Of course it still needs privileges on the cluster but we don’t have to give an external tool access to our cluster which is a big advantage.
More information: