I'm currently migrating an existing CI/CD pipeline build in Azure DevOps from the ‘classic’ build approach to YAML files. I already talked about the concept of templates as a replacement for Task groups in the 'classic' pipeline and the multiple ways it can be used.
Before I finally shut up about templates(no promised made) I want to talk about one extra related feature I didn’t mention yet. One extra advantage that you get when you extend from a template (next to re-use) is that you can enforce a specific pipeline usage.
This can be done by introducing a Required template check.
Required template check
With the required template check, you can enforce pipelines to use a specific YAML template. When this check is in place, a pipeline will fail if it doesn't extend from the referenced template.
in your Azure DevOps project, go to the environment where you want to add the extra check.
Click on the ‘+’ sign to add a new approval.
Select Required template from the list and click Next.
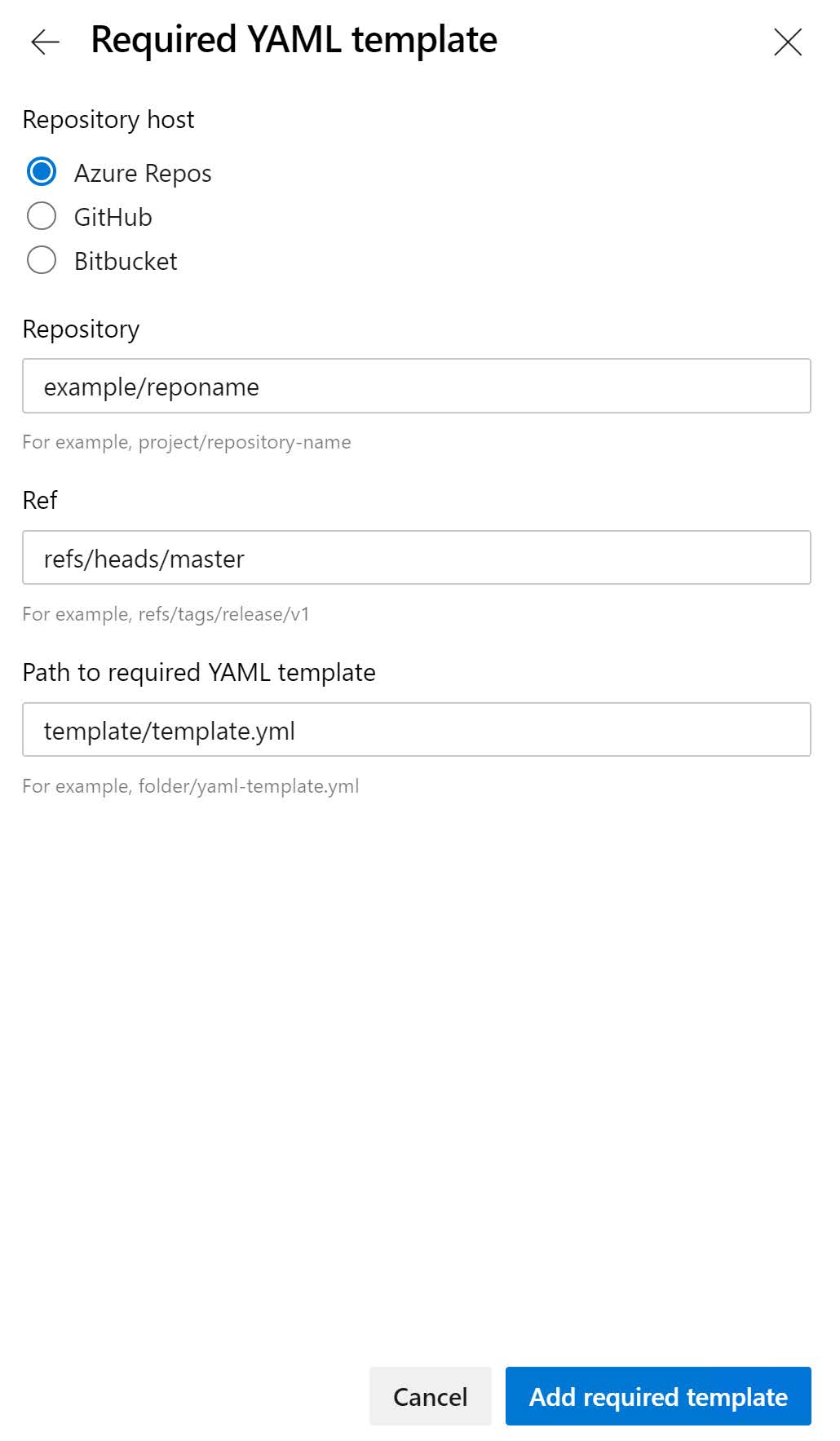
On the Required template screen, click on the ‘+’ sign to specify the required template.
Now enter the details to get to your required template file.
- Repository type: The location of your repository (GitHub, Azure, or Bitbucket).
- Repository: The name of your repository that contains your template.
- Ref: The branch or tag of the required template.
- Path to required template: The name of your template.
Click on Add required template to add the template.
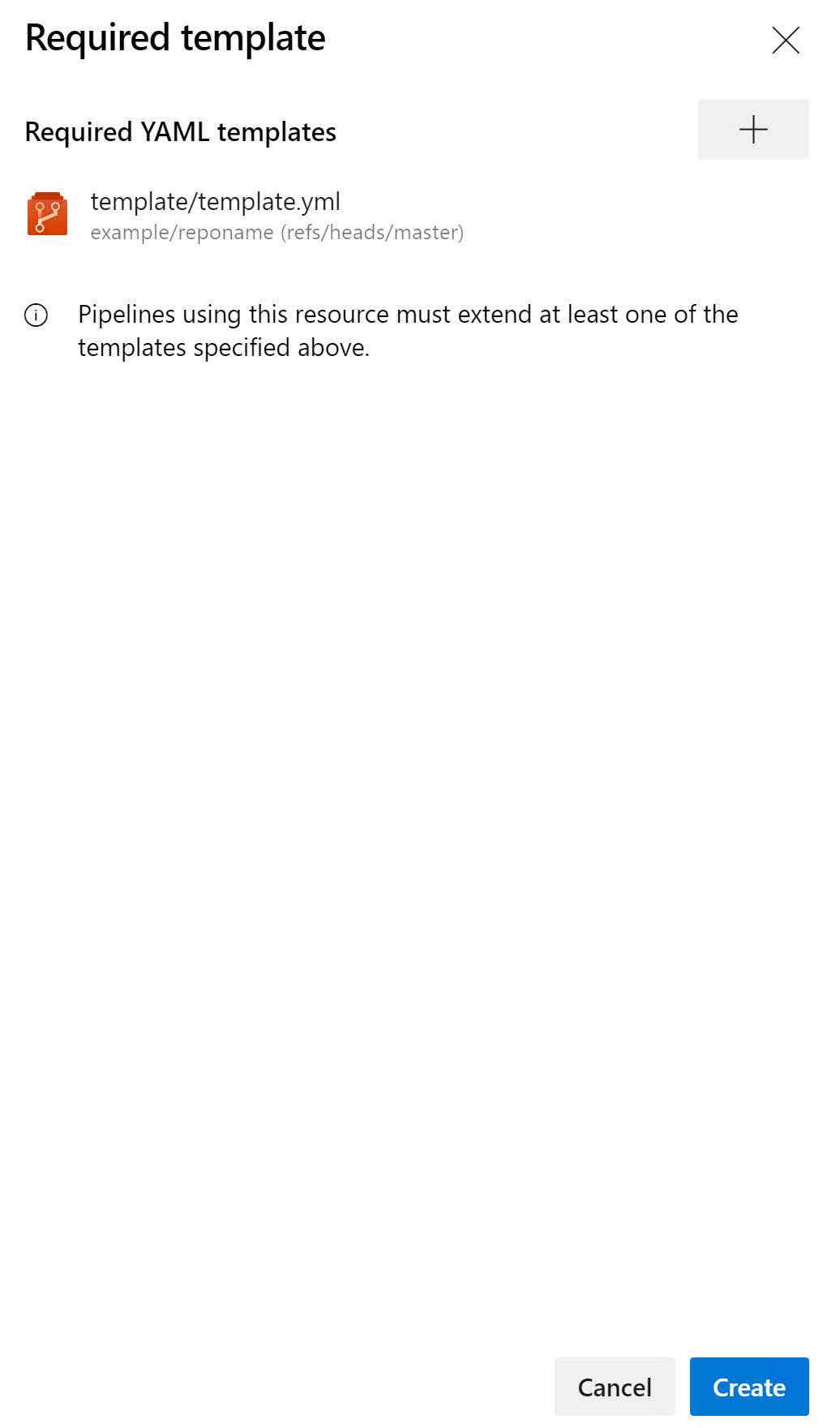
Remark: You can have multiple required templates for the same environment
Once you have selected your template, you can click Create to create the new check.
Now you are good to go!