The OWASP Dependency-Check tool is a free open-source Software Composition Analysis (SCA) tool that attempts to detect publicly disclosed vulnerabilities contained within a project's dependencies. It does this by determining if there is a Common Platform Enumeration (CPE) identifier for a given dependency.
In this post I’ll show you how to integrate this in your Azure DevOps build pipeline using the OWASP Dependency Check task.
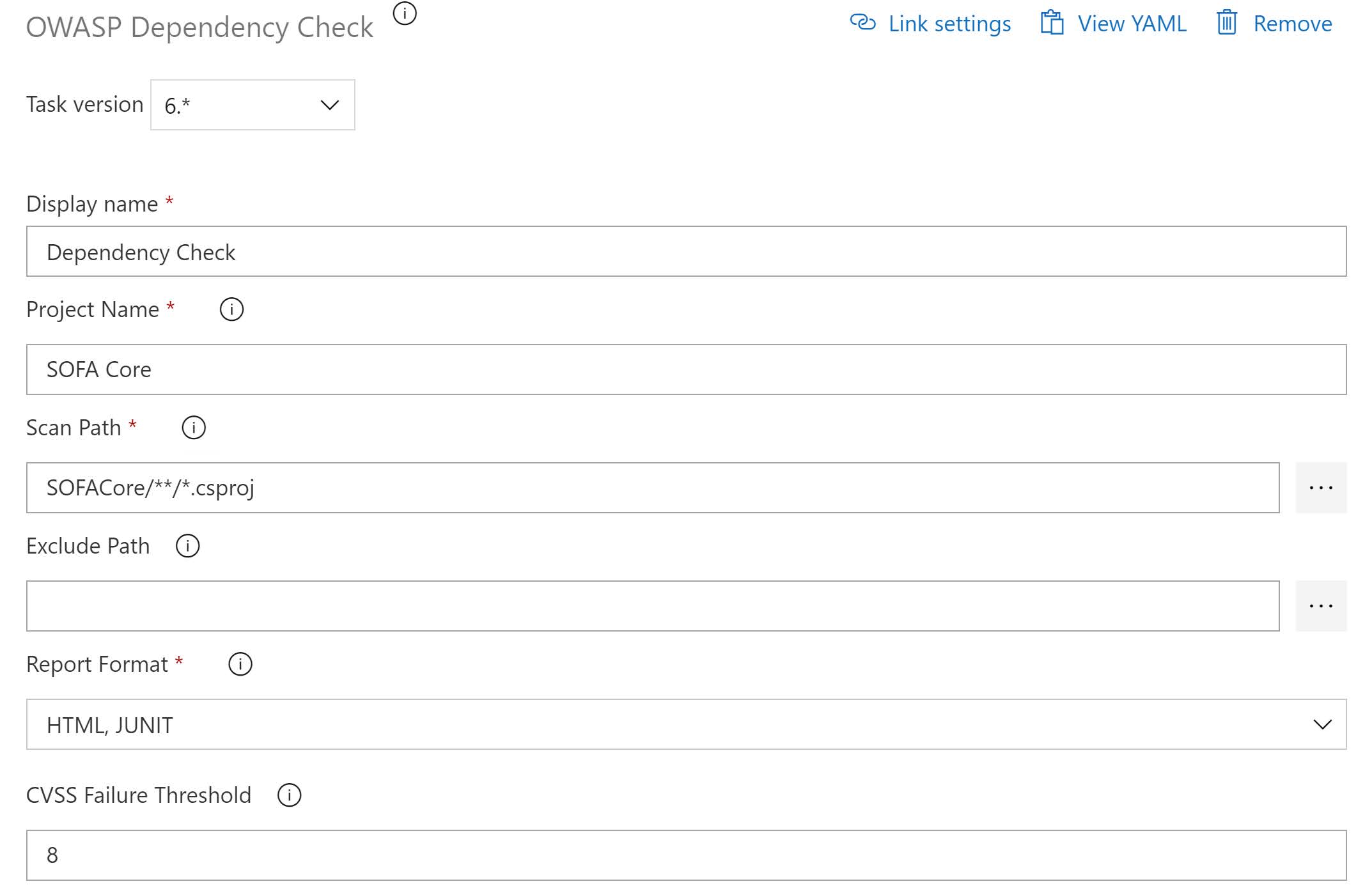
After installing the OWASP Dependency Check extension in your Azure DevOps instance, you have a new task available:
To use it with a C# project, set the scan path to your csproj folders:
In the example above I configured multiple report output formats.
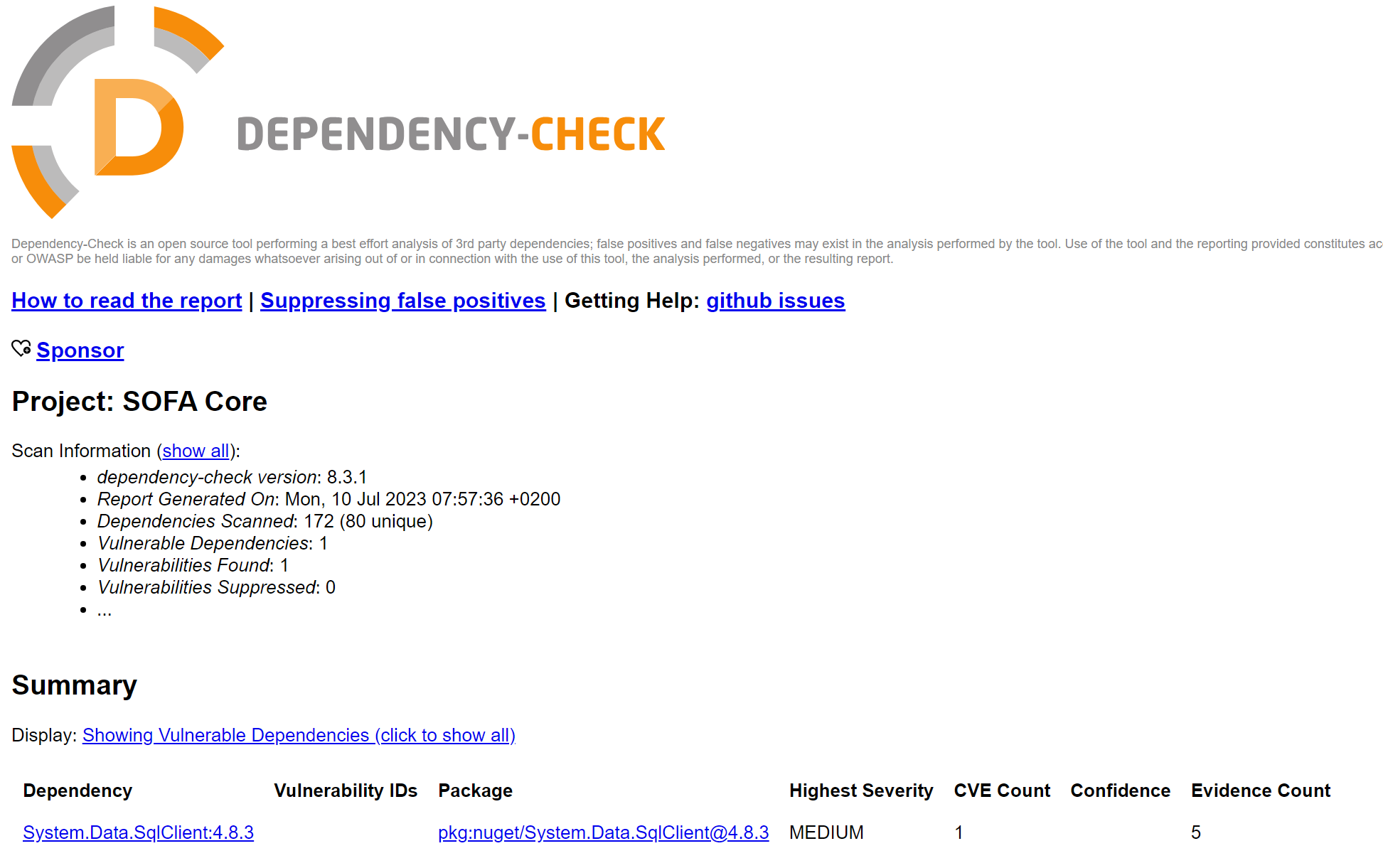
Here is the HTML output I got after executing the build:
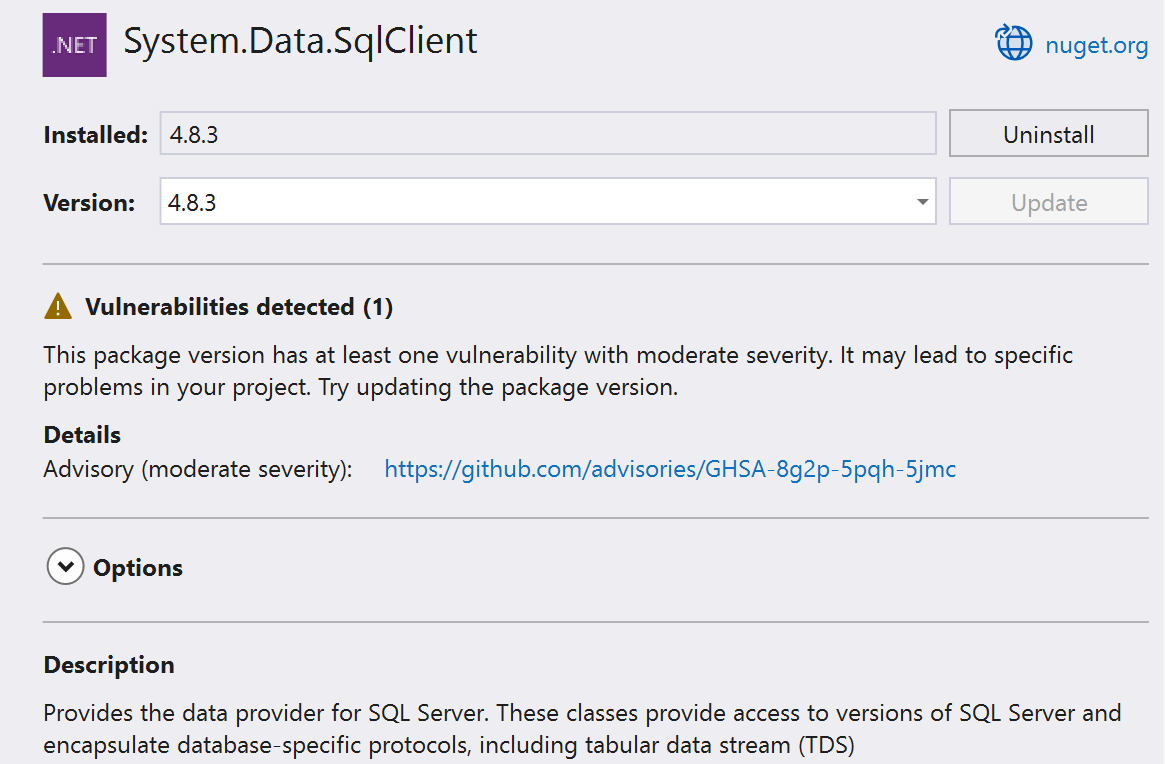
It mentions one vulnerability. And indeed when I go to the Package Manager view in Visual Studio, I noticed that the used version was flagged:
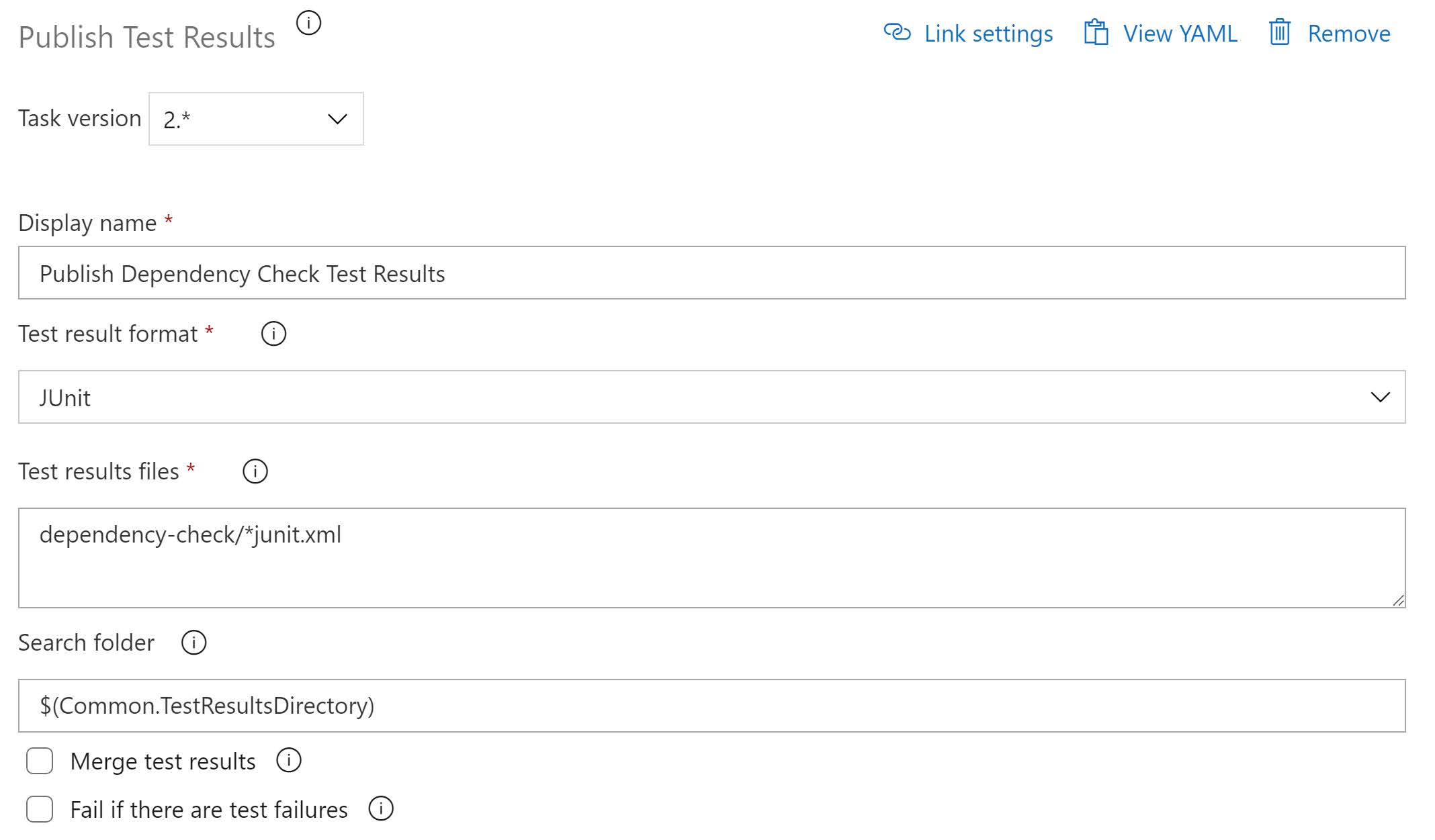
If you want to consume the results inside Azure DevOps, you have the option to output the results in the JUnit format and import the published test results:
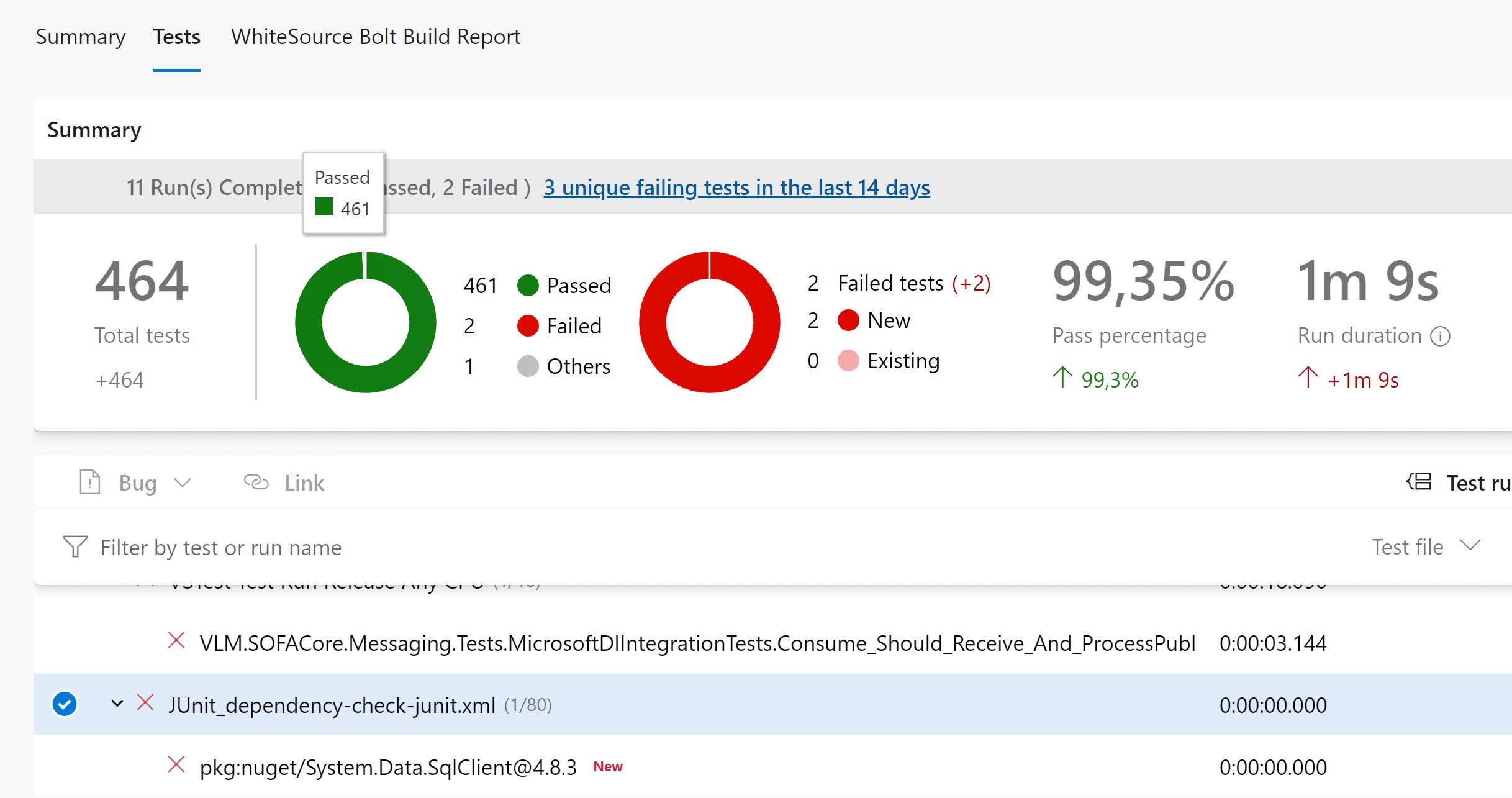
These results are then available as part of the Test output: