Note: This is a continuation of a previous post found here: https://bartwullems.blogspot.com/2018/06/tfs-build-agent-ssl-certificate-problem.html
In the previous post I suggested a solution which disables the SSL verification check. Of course, this is more a dirty heck and not a great solution at all. Let’s have a look at a better solution:
Step 1 - Extract the root certificate
Browse to your TFS portal. Inside the browser go to the SSL certificate(exact steps can differ depending on your browser of choice; here are the steps for Chrome: https://bartwullems.blogspot.com/2017/05/how-can-i-view-used-ssl-certificate-in.html)
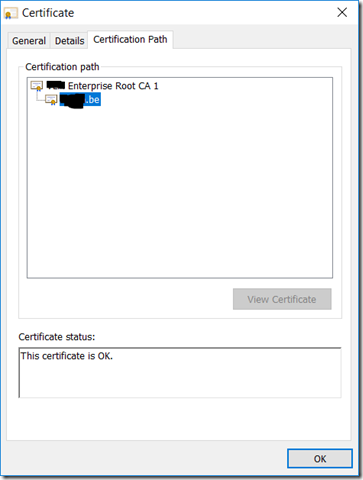
Once you have the certificate window open, go to the Certification Path tab and select the top-most certificate in the chain.
Click View Certificate, go to the Details tab and click on the Copy to File… button.
The export wizard will be started start the export wizard for certificates. On the second page of the wizard, you will be asked what format to use for exporting your certificate. Choose the second option: base64 encoded X.509.
Click Next, specify a file name and save the certificate to disk.
Step 2 – Create a copy of the Git certificate store
Browse to the location of the git certificate store(on my machine this is C:\Program Files\Git\usr\ssl\certs). Copy the ca-bundle.crt to your user profile directory (%USERPROFILE%) alongside your user .gitconfig file.
Step 3 – Add the root certificate to the Git certificate store
Open the exported certificate, copy its entire content to the clipboard. Afterwards open the copy of the ca-bundle.crt file and paste the exported certificate content to the end of this file.
Step 4 – Configure git to use the Git certificate store copy
Execute the following command to point git to your private copy of the certificate store:
git config --global http.sslCAInfo C:/Users/yourname/ca-bundle.crt