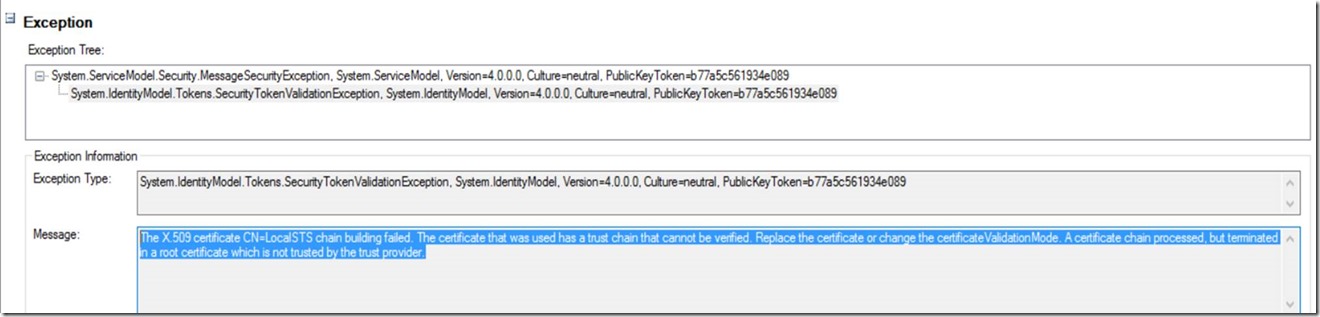
SecurityTokenValidation exception: the X.509 certificate CN=LocalSTS chain building failed. The certificate that was used has a trust chain that cannot be verified.
I’m talking to a WCF service and use a bearer token to authenticate to the service. The bearer token is provided by a custom STS (during testing). However when I tried to invoke the service, I got the following error message back:
The X.509 certificate CN=LocalSTS chain building failed. The certificate that was used has a trust chain that cannot be verified. Replace the certificate or change the certificateValidationMode. A certificate chain processed, but terminated in a root certificate which is not trusted by the trust provider.
And indeed this error makes sense as the tokens generated by the local STS are signed by an untrusted certificate. As we are using it for testing purposes only, it’s OK to disable the certificate validation.
- Open the configuration of your webservice.
- Add a serviceCredentials block to your serviceBehavior.
- Inside this block add an issuedTokenAuthentication section and set the certificateValidationMode to “None”.
- That should do the trick.
- Note that this should only be done for testing purposed and this is not secure for production usage!
<behaviors>
<serviceBehaviors>
<behavior name="">
<serviceMetadata httpGetEnabled="true" httpsGetEnabled="true" />
<serviceDebug includeExceptionDetailInFaults="false" />
<serviceAuthorization principalPermissionMode="Always" />
<serviceCredentials>
<issuedTokenAuthentication certificateValidationMode="None" />
</serviceCredentials>
</behavior>
</serviceBehaviors>
</behaviors>