I’m currently working on a training for one of my customers covering WIF(Windows Identity Foundation), OIDC(Open ID Connect) and some other security related topics on top of the .NET stack.
Yesterday I got a strange problem after configuring the MVC application that should act as the relying party.
Here is the WIF specific configuration:
And here is the error I got when I ran the application:
ID4175: The issuer of the security token was not recognized by the IssuerNameRegistry. To accept security tokens from this issuer, configure the IssuerNameRegistry to return a valid name for this issuer.
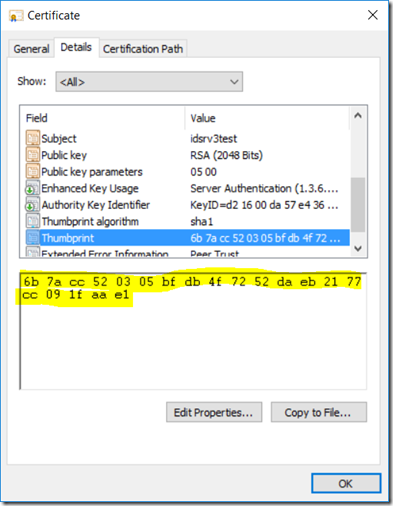
I compared the thumbprint of the certificate used by the STS with the thumbprint inside the config:
<trustedIssuers>
<add thumbprint="6b 7a cc 52 03 05 bf db 4f 72 52 da eb 21 77 cc 09 1f aa e1" />
</trustedIssuers>
No matter how much I looked, I couldn’t see a difference.
Time to ask the global web for help. After some research I found the following article: https://support.microsoft.com/en-us/kb/2023835
It seems there is a bug in the Richedit control that is used by the Certificate UI. When you copy the thumbprint, an extra (invisible) unicode character is being copied also. And indeed when I typed it in instead of copying it over, the error disappeared…