There are 2 ways to start using Application Insights in your applications:
- Option 1: You install and add the Application Insights SDK to your application. This is easy thanks to the Visual Studio integration but requires you to open, configure and release each application separately
- Option 2: Use the Application Insights Status Monitor tool. This tool allows you to instrument a live web app with Visual Studio Application Insights, without having to modify or redeploy your code.
Remark: Note there is a third option through the Application Insights extension but this only applies to applications hosted on Azure.
After installing the Application Insights Status Monitor tool, you can pick the installed web applications that you want to monitor. Of course, ‘real’ administrators don’t use a UI but choose Powershell instead . Application Insights supports this through the Microsoft.Diagnostics.Agent.StatusMonitor.PowerShell.dll module.
Here is an example how to use it:
- Open a Powershell command prompt.
- Load the Application Insights Powershell module
- Import-Module 'C:\Program Files\Microsoft Application Insights\Status Monitor\PowerShell\Microsoft.Diagnostics.Agent.StatusMonitor.PowerShell.dll'
- If you get an error that the module could not be loaded, check your Powershell version (use the $PSVersionTable variable). Probably you have to update it first.
- Go to the Azure Portal
- Create a new Application Insights subscription
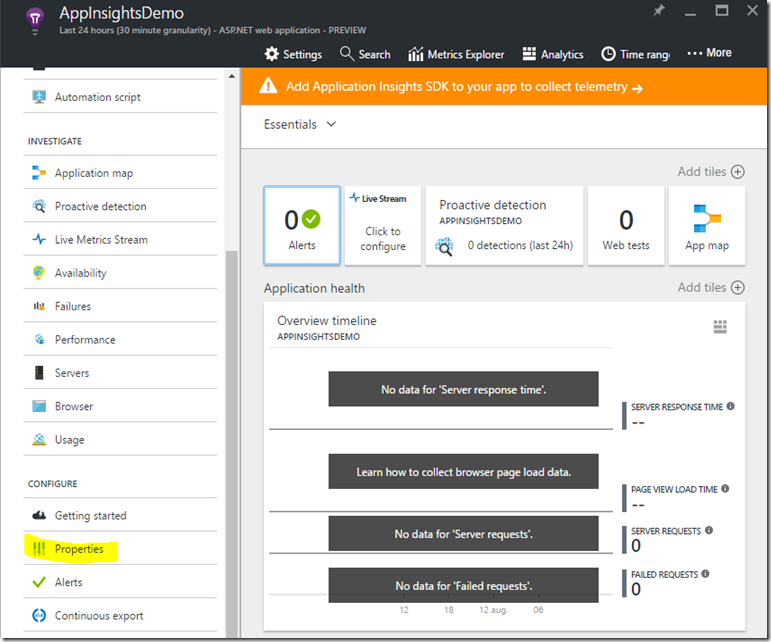
- Once created click on Properties
- Copy the Instrumentation key from the Properties page. This key is required to link your web application to the Application Insights resource.
- Go back to your Powershell command line
- Type the following command to start monitoring an application
Start-ApplicationInsightsMonitoring -Name appName -InstrumentationKey 00000000-000-000-000-0000000Hereby is -Namethe name of the app in IIS and-InstrumentationKey the ikey of the Application Insights resource where you want the results to be displayed.- After doing this, you can check which applications are monitored using following command
- Get-ApplicationInsightsMonitoringStatus