Last week I had some fun investigating a WIF issue. A colleague came to me and explained the following situation:
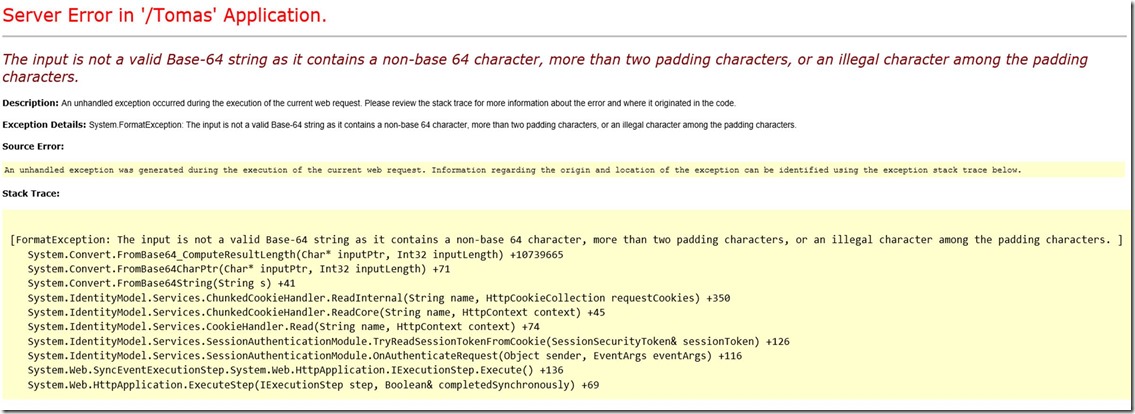
I have 2 sites under the same domain each configured as a separate application in IIS with their own applicationpool. Site 1 is available at my.domain.name/Site1. The other site is available at my.domain.name/Portal/Site2. When I login to site 1 through ADFS everything is ok. Then I go to site 2 where I also login. When I then move back to Site 1, I get the following error message:
The input is not a valid Base-64 string as it contains a non-base 64 character, more than two padding characters, or an illegal character among the padding characters.
When I investigated the issue, I noticed that the “same” FedAuth cookie was issued twice, once scoped to my.domain.name/Site1, once scoped to the root domain my.domain.name. When browsing back to Site1, WIF get both cookies(as both apply to the target domain). However as both cookies are issued for different websites, combining them results in an invalid cookie, explaining the error message above.
To solve this we had to change the WIF configuration to scope the cookie correctly:
The original config:
<system.identityModel.services>
<federationConfiguration>
<cookieHandler requireSsl="true" />
<wsFederation passiveRedirectEnabled="false" issuer="https://adfs2/adfs/ls/" realm="https://my.domain.name/site1/" requireHttps="true" />
</federationConfiguration>
</system.identityModel.services>
The updated config:
<system.identityModel.services>
<federationConfiguration>
<cookieHandler path="/" requireSsl="true" />
<wsFederation passiveRedirectEnabled="false" issuer="https://adfs2/adfs/ls/" realm="https://my.domain.name/site1/" requireHttps="true" />
</federationConfiguration>
</system.identityModel.services>
After doing that, we got an other error instead:
ID4291: The security token ‘System.IdentityModel.Tokens.SessionSecurityToken’ is not scoped to the current endpoint.
This error is caused by the fact that both sites are using a different application pool. To solve this second error, there are 2 possible solutions:
Solution 1
Run both sites using the same application pool.
Solution 2
Update your WIF configuration to use the MachineKeySessionSecurityTokenHandler instead of the default SessionSecurityTokenHandler:
<system.identityModel>
<identityConfiguration>
<securityTokenHandlers>
<remove type="System.IdentityModel.Tokens.SessionSecurityTokenHandler, System.IdentityModel, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089" />
<add type="System.IdentityModel.Services.Tokens.MachineKeySessionSecurityTokenHandler, System.IdentityModel.Services, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089" />
</securityTokenHandlers>
</identityConfiguration>
</system.identityModel>
![clip_image001[5] clip_image001[5]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEiUlPbJ62-yXcahMNUVa6sfAxlW7VsPeDM4dTHiPXvWL4qSxm1D2kcdcDpwdZXeWrflDOvL6pMdrlsMj6FmD9AdKeaEY3JXYnRRFuwTJ7msiWGKZgPUaUDwUmJirijraBhzygZHsiMhxGXf/?imgmax=800)